Consider the following instructions to learn how to trust a public SSL/TLS-certificate to enable an encrypted connection. For example, these steps could be necessary for self-signed certificates which are generally classified as not trusted.
Export certificates
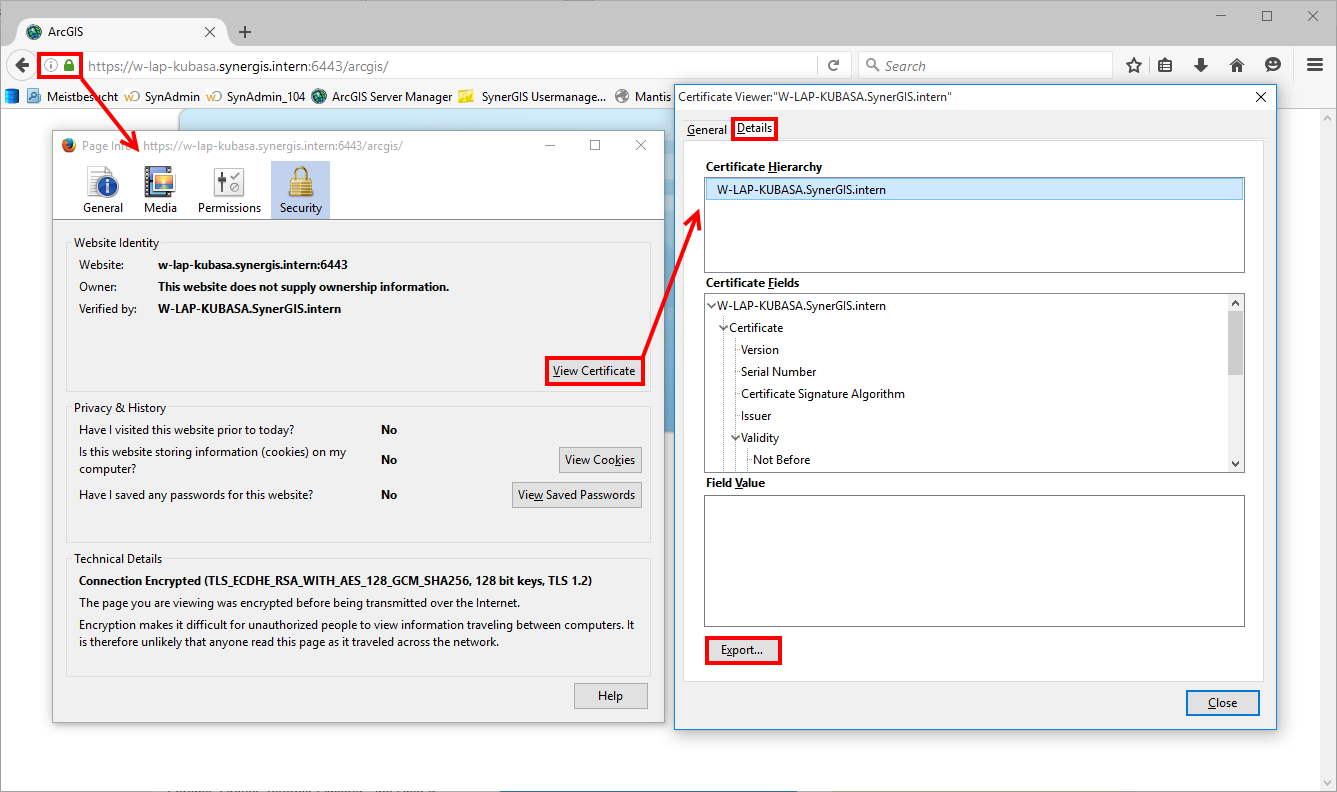
Within Mozilla Firefox it is possible to regard and export an appropriate certificate. Therefor, open the respective site in Mozilla Firefox and open the certificate via the lock-symbol on the left side of the URL bar (after entering to an unsafe website has been confirmed). Afterwards, you can export the appropriate certificate as a *.crt-file. For example
Windows
Please consider the following steps for importing a (self-signed) SSL/TLS-certificate to the list of trusted certificates, which is used by Windows (this means, that this is also used by Internet Explorer and WebOffice author):
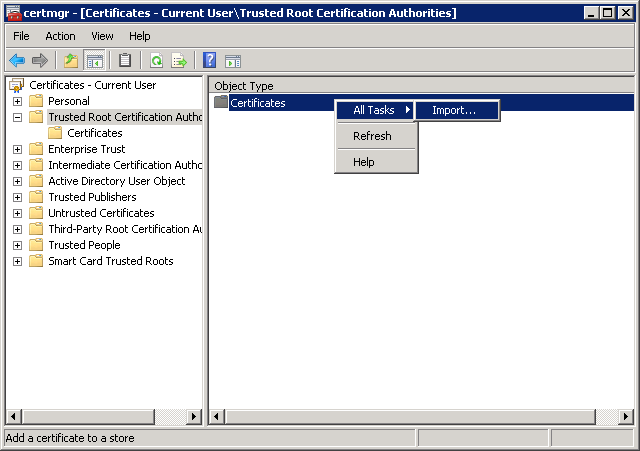
▪Open the Command Prompt (Run as administrator) and start the tool certmgr.
▪Navigate to Trusted Root Certification Authorities
▪Click on Certificates with the right mouse button --> All Tasks --> Import...
▪Import the appropriate certificate (*.crt-file, which was exported like described in the paragraph above)
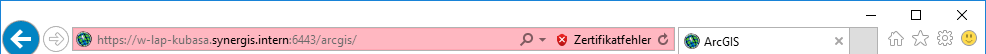
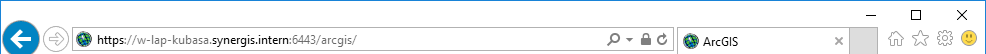
Afterwards, the appropriate URL is ready to be tested with Internet Explorer - no certificate error should appear anymore. For comparison:
Display of the URL bar in Internet Explorer before importing the appropriate certificate:
Display of the URL bar in Internet Explorer after importing the appropriate certificate:
Java
There is also the Java-Truststore, which includes a list of all trusted certificates which are used by Java-based programs like WebOffice Server. The default name of the Java Truststore is cacerts and it is secured by the password changeit. Due to the fact that each JRE has its own Truststore, you will have to determine the appropriate version of Java first. This can be checked via SynAdmin --> System:
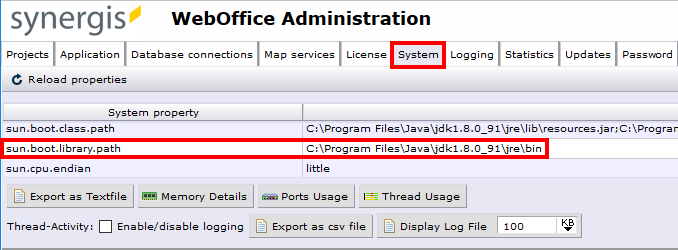
According to the example above, the appropriate Truststore is located under C:\Program Files\Java\jdk1.8.0_91\jre\lib\security.
The appropriate certificates can now be imported by using the KeyStoreExplorer tool (http://www.keystore-explorer.org/):
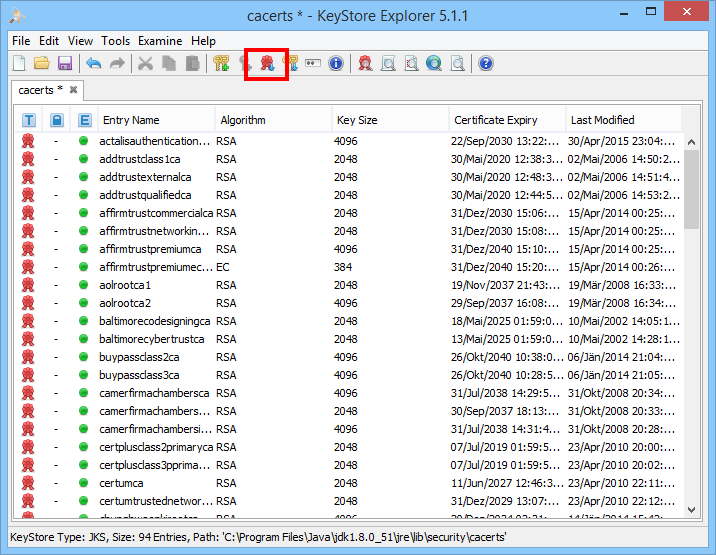
Note: Although the appropriate certificate was imported by using the KeyStoreExplorer tool, you cannot verify the success of this importing process neither in the Internet Explorer nor in Mozilla Firefox. Both web-browsers are not using the Java-Truststore - they have their own lists of certificates (e.g. Internet Explorer is using the appropriate list of Windows).
ArcGIS Server
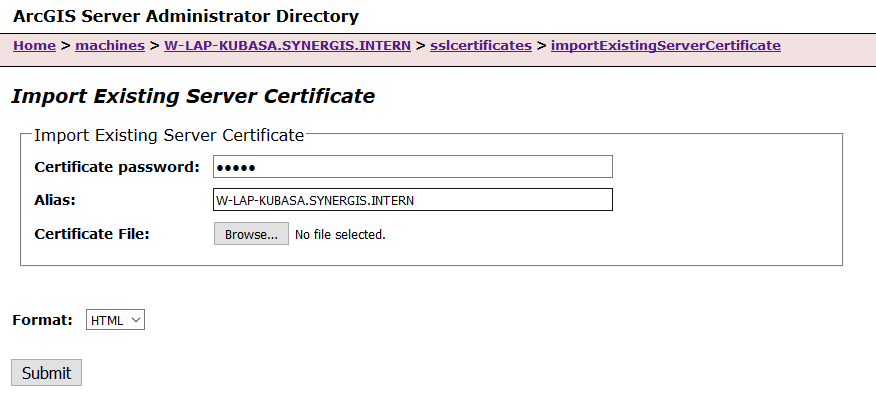
You also have to import the appropriate self-signed certificate to the ArcGIS Server, when it is running under a secured connection, too. Therefor, please open the ArcGIS Server Admin interface in your web-browser and navigate to Machines --> <Name of the registered machine> --> sslcertificates --> importExistingServerCertificate. In the following dialogue you have to insert a valid password and an alias for the appropriate certificate. Search for the respective certificate via the Browse... button and upload it by clicking the Submit button.
To be able to request the map services from the respective ArcGIS Server in WebOffice author (for example within the diverse wizards), it is important to use precisely the server URL issued to the certificate. Otherwise you will get the following error message after requesting the appropriate map services:
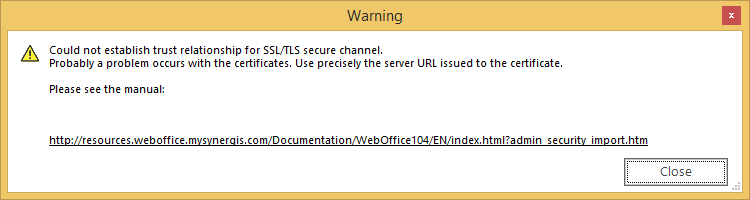
Note: For example: https://<hostname>:6443/arcgis is not working. In comparison, https://<hostname>.domain.com:6443/arcgis is working properly, because the self-signed certificate was created for <hostname>.domain.com.